Right this moment, we’re saying digital non-public cloud (VPC) encryption controls, a brand new functionality of Amazon Digital Non-public Cloud (Amazon VPC) that helps you audit and implement encryption in transit for all visitors inside and throughout VPCs in a Area.
Organizations throughout monetary providers, healthcare, authorities, and retail face important operational complexity in sustaining encryption compliance throughout their cloud infrastructure. Conventional approaches require piecing collectively a number of options and managing advanced public key infrastructure (PKI), whereas manually monitoring encryption throughout totally different community paths utilizing spreadsheets—a course of vulnerable to human error that turns into more and more difficult as infrastructure scales.
Though AWS Nitro primarily based cases routinely encrypt visitors on the {hardware} layer with out affecting efficiency, organizations want easy mechanisms to increase these capabilities throughout their total VPC infrastructure. That is significantly essential for demonstrating compliance with regulatory frameworks resembling Well being Insurance coverage Portability and Accountability (HIPAA), Fee Card Trade Knowledge Safety Customary (PCI DSS), and Federal Danger and Authorization Administration Program (FedRAMP), which require proof of end-to-end encryption throughout environments. Organizations want centralized visibility and management over their encryption standing, with out having to handle efficiency trade-offs or advanced key administration methods.
VPC encryption controls handle these challenges by offering two operational modes: monitor and implement. In monitor mode, you’ll be able to audit the encryption standing of your visitors flows and determine assets that enable plaintext visitors. The function provides a brand new encryption-status subject to VPC circulate logs, providing you with visibility into whether or not visitors is encrypted utilizing Nitro {hardware} encryption, application-layer encryption (TLS), or each.
After you’ve recognized assets that want modification, you’ll be able to take steps to implement encryption. AWS providers, resembling Community Load Balancer, Utility Load Balancer, and AWS Fargate duties, will routinely and transparently migrate your underlying infrastructure to Nitro {hardware} with none motion required from you and with no service interruption. For different assets, such because the earlier era of Amazon Elastic Compute Cloud (Amazon EC2) cases, you have to to modify to fashionable Nitro primarily based occasion sorts or configure TLS encryption at utility degree.
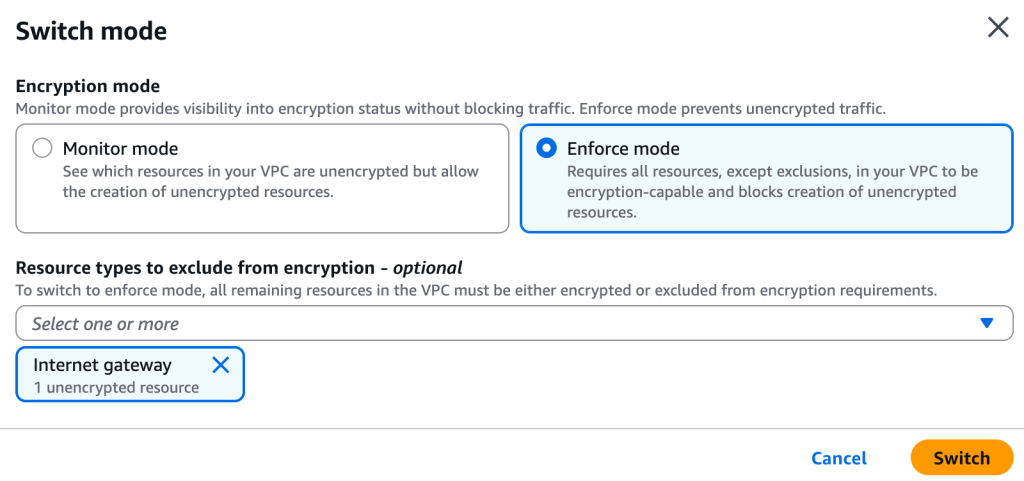
You may swap to implement mode in spite of everything assets have been migrated to encryption-compliant infrastructure. This migration to encryption-compliant {hardware} and communication protocols is a prerequisite for enabling implement mode. You may configure particular exclusions for assets resembling web gateways or NAT gateways, that don’t help encryption (as a result of the visitors flows exterior of the AWS community).
Different assets have to be encryption-compliant and may’t be excluded. After activation, implement mode offers that every one future assets are solely created on suitable Nitro cases, and unencrypted visitors is dropped when incorrect protocols or ports are detected.
Let me present you get began
For this demo, I began three EC2 cases. I exploit one as an internet server with Nginx put in on port 80, serving a transparent textual content HTML web page. The opposite two are constantly making HTTP GET requests to the server. This generates clear textual content visitors in my VPC. I exploit the m7g.medium occasion kind for the online server and one of many two purchasers. This occasion kind makes use of the underlying Nitro System {hardware} to routinely encrypt in-transit visitors between cases. I exploit a t4g.medium occasion for the opposite net shopper. The community visitors of that occasion just isn’t encrypted on the {hardware} degree.
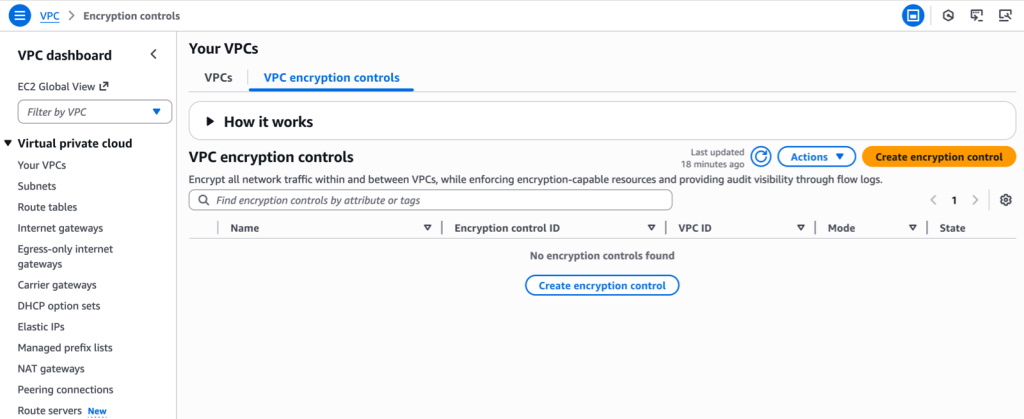
To get began, I allow encryption controls in monitor mode. Within the AWS Administration Console, I choose Your VPCs within the left navigation pane, then I swap to the VPC encryption controls tab. I select Create encryption management and choose the VPC I need to create the management for.
Every VPC can have just one VPC encryption management related to it, making a one-to-one relationship between the VPC ID and the VPC encryption management Id. When creating VPC encryption controls, you’ll be able to add tags to assist with useful resource group and administration. You may also activate VPC encryption management while you create a brand new VPC.
I enter a Title for this management. I choose the VPC I need to management. For current VPCs, I’ve to begin in Monitor mode, and I can activate Implement mode after I’m positive there isn’t any unencrypted visitors. For brand spanking new VPCs, I can implement encryption on the time of creation.
Optionally, I can outline tags when creating encryption controls for an current VPC. Nonetheless, when enabling encryption controls throughout VPC creation, separate tags can’t be created for VPC encryption controls—as a result of they routinely inherit the identical tags because the VPC. After I’m prepared, I select Create encryption management.
 Alternatively, I can use the AWS Command Line Interface (AWS CLI):
Alternatively, I can use the AWS Command Line Interface (AWS CLI):
aws ec2 create-vpc-encryption-control --vpc-id vpc-123456789Subsequent, I audit the encryption standing of my VPC utilizing the console, command line, or circulate logs:
aws ec2 create-flow-logs
--resource-type VPC
--resource-ids vpc-123456789
--traffic-type ALL
--log-destination-type s3
--log-destination arn:aws:s3:::vpc-flow-logs-012345678901/vpc-flow-logs/
--log-format '${flow-direction} ${traffic-path} ${srcaddr} ${dstaddr} ${srcport} ${dstport} ${encryption-status}'
{
"ClientToken": "F7xmLqTHgt9krTcFMBHrwHmAZHByyDXmA1J94PsxWiU=",
"FlowLogIds": [
"fl-0667848f2d19786ca"
],
"Unsuccessful": []
}After a couple of minutes, I see this visitors in my logs:
flow-direction traffic-path srcaddr dstaddr srcport dstport encryption-status
ingress - 10.0.133.8 10.0.128.55 43236 80 1 # <-- HTTP between net shopper and server. Encrypted at hardware-level
egress 1 10.0.128.55 10.0.133.8 80 43236 1
ingress - 10.0.133.8 10.0.128.55 36902 80 1
egress 1 10.0.128.55 10.0.133.8 80 36902 1
ingress - 10.0.130.104 10.0.128.55 55016 80 0 # <-- HTTP between net shopper and server. Not encrypted at hardware-level
egress 1 10.0.128.55 10.0.130.104 80 55016 0
ingress - 10.0.130.104 10.0.128.55 60276 80 0
egress 1 10.0.128.55 10.0.130.104 80 60276 010.0.128.55is the online server with hardware-encrypted visitors, serving clear textual content visitors at utility degree.10.0.133.8is the online shopper with hardware-encrypted visitors.10.0.130.104is the online shopper with no encryption on the {hardware} degree.
The encryption-status subject tells me the standing of the encryption for the visitors between the supply and vacation spot handle:
- 0 means the visitors is in clear textual content
- 1 means the visitors is encrypted on the community layer (Stage 3) by the Nitro system
- 2 means the visitors is encrypted on the utility layer (Level7, TCP Port 443 and TLS/SSL)
- 3 means the visitors is encrypted each on the utility layer (TLS) and the community layer (Nitro)
- “-” means VPC encryption controls usually are not enabled, or AWS Circulation Logs don’t have the standing data.
The visitors originating from the online shopper on the occasion that isn’t Nitro primarily based (10.0.130.104), is flagged as 0. The visitors initiated from the online shopper on the Nitro- ased occasion (10.0.133.8) is flagged as 1.
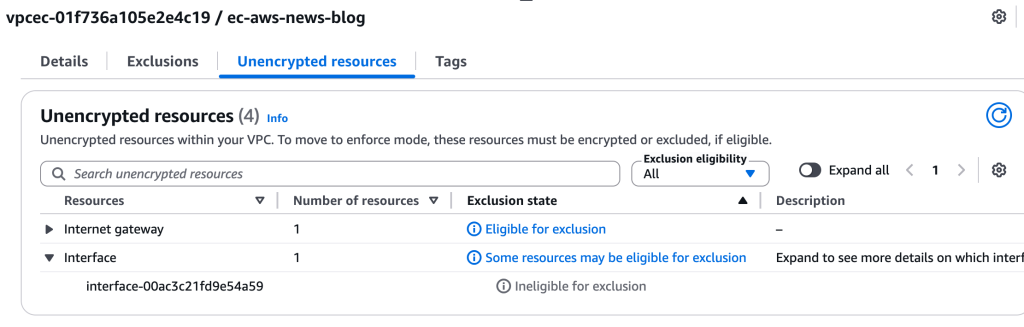
I additionally use the console to determine assets that want modification. It stories two nonencrypted assets: the web gateway and the elastic community interface (ENI) of the occasion that isn’t primarily based on Nitro.
 I may also examine for nonencrypted assets utilizing the CLI:
I may also examine for nonencrypted assets utilizing the CLI:
aws ec2 get-vpc-resources-blocking-encryption-enforcement --vpc-id vpc-123456789After updating my assets to help encryption, I can use the console or the CLI to modify to implement mode.
Within the console, I choose the VPC encryption management. Then, I choose Actions and Change mode.
aws ec2 modify-vpc-encryption-control --vpc-id vpc-123456789 --mode implementHow one can modify the assets which are recognized as nonencrypted?
All of your VPC assets should help visitors encryption, both on the {hardware} layer or on the utility layer. For many assets, you don’t must take any motion.
AWS providers accessed by AWS PrivateLink and gateway endpoints routinely implement encryption on the utility layer. These providers solely settle for TLS-encrypted visitors. AWS will routinely drop any visitors that isn’t encrypted on the utility layer.
If you allow monitor mode, we routinely and regularly migrate your Community Load Balancers, Utility Load Balancers, AWS Fargate clusters, and Amazon Elastic Kubernetes Service (Amazon EKS) clusters to {hardware} that inherently helps encryption. This migration occurs transparently with none motion required from you.
Some VPC assets require you to pick the underlying cases that help fashionable Nitro hardware-layer encryption. These embody EC2 Situations, Auto Scaling teams, Amazon Relational Database Service (Amazon RDS) databases (together with Amazon DocumentDB), Amazon ElastiCache node-based clusters, Amazon Redshift provisioned clusters, EKS clusters, ECS with EC2 capability, MSK Provisioned, Amazon OpenSearch Service, and Amazon EMR. Emigrate your Redshift clusters, you will need to create a brand new cluster or namespace from a snapshot.
If you happen to use newer-generation cases, you possible have already got encryption-compliant infrastructure as a result of all latest occasion sorts help encryption. For older-generation cases that don’t help encryption-in transit, you’ll must improve to supported occasion sorts.
Issues to know when utilizing AWS Transit Gateway
When your VPCs with encryption controls enabled are related by way of a Transit Gateway, you’ll must manually activate encryption controls on the Transit Gateway to encrypt visitors between the VPCs. This may be finished utilizing the AWS console, the modify-transit-gateway command or API. Enabling encryption on an current Transit Gateway gained’t disrupt the visitors flowing between VPCs connected to the Transit Gateway.
When a Transit Gateway and its connected VPCs have encryption controls in implement mode (with no exclusions), visitors is encrypted end-to-end.
When making a Transit Gateway by AWS CloudFormation with encryption help enabled, you want one extra AWS Identification and Entry Administration (IAM) permission: ec2:ModifyTransitGateway. This permission is required as a result of CloudFormation makes use of a two-step course of to create a Transit Gateway. It first creates the Transit Gateway with fundamental configuration, then calls ModifyTransitGateway to allow encryption help. With out this permission, your CloudFormation stack will fail throughout creation when trying to use the encryption configuration, even in case you’re solely performing what seems to be a create operation.
Pricing and availability
You can begin utilizing VPC encryption controls at the moment in these AWS Areas: US East (Ohio, N. Virginia), US West (N. California, Oregon), Africa (Cape City), Asia Pacific (Hong Kong, Hyderabad, Jakarta, Melbourne, Mumbai, Osaka, Singapore, Sydney, Tokyo), Canada (Central), Canada West (Calgary), Europe (Frankfurt, Eire, London, Milan, Paris, Stockholm, Zurich), Center East (Bahrain, UAE), and South America (São Paulo).
VPC encryption controls is freed from price till March 1, 2026. The VPC pricing web page can be up to date with particulars as we get nearer to that date.
To study extra, go to the VPC encryption controls documentation or attempt it out in your AWS account. I sit up for listening to how you utilize this function to strengthen your safety posture and make it easier to meet compliance requirements.