Organizations together with the U.S. army, are more and more adopting cloud deployments for his or her flexibility and price financial savings in deployment. One side of such deployments is the shared safety mannequin promulgated by NSA, which describes most of the safety companies that cloud service suppliers (CSPs) help and offers for cooperation on safety points. This mannequin additionally leaves safety obligations on the organizations contracting for service. These obligations embody making certain the hosted utility is undertaking its meant function for the approved set of customers.
Cloud circulation logs, as recognized by community defenders, are a worthwhile supply of information to help this safety duty. If anticipated occasions (indicated by switch of information to and from the cloud) occur, these logs assist determine which exterior endpoints obtain service, the extent of the service, and whether or not there are customers who overuse cloud sources.
The SEI has a protracted historical past of help for circulation log evaluation, together with its early 2025 releases (for Azure or AWS) of open-source scripts to facilitate cloud circulation log evaluation. This weblog summarizes these efforts and explores challenges related to correlating occasions throughout a number of CSPs.
Gathering Cloud Movement Logs
A cloud circulation log is a group of information that include summaries of community visitors to and from endpoints within the cloud. Hosts within the cloud are particularly configured to supply and devour packets of information throughout the web. That is not like on-premises circulation technology, which is finished for all hosts on a given community based mostly on sensors. Hosts (digital non-public clouds or community safety teams) or subnets (VNets) within the cloud might generate these circulation information. Whereas not essentially meant for long-term retention for assessing safety, these logs cowl a historical past of cloud exercise with out respect to malware or alert signatures or any particular community occasions. This historical past offers context for detected occasions and profiles of anticipated, anomalous, or malicious exercise. This context helps extra dependable interpretation of alerts and community experiences, which finally makes organizations safer.
Ongoing assortment additionally permits for identification of three types of visitors observations:
- Occasions—remoted behaviors with safety implications, together with benign (assuring that one thing is occurring that ought to occur) and malicious (figuring out that one thing is occurring that compromises safety)
- Patterns—collections of occasions which will represent proof of a defensive measure or an aggressive motion. Generally, patterns are collections of a couple of occasion and supply context for evaluating actions.
- Developments—sequences of occasions that cumulatively determine shifts in community habits (once more, cumulatively benign or cumulatively malicious)
Approaches to Analyzing Cloud Movement Logs
Cloud service suppliers provide a wide range of assortment choices and report contents. For examples see Desk 1, which is mentioned under. The gathering choices embody the interval for which the information combination community visitors (e.g., 1-minute or 5-minute intervals) and the sampling employed within the aggregation (e.g., all packets or a pattern of 1 packet from every ten). These variations can complicate comparability or integration throughout CSPs. Assumptions made by CSPs, akin to assumed visitors route, may complicate evaluation of the community visitors. If the evaluation course of doesn’t tackle these variations, fusion of information from completely different clouds turns into troublesome and outcomes enhance in uncertainty. Whereas evaluation of cloud circulation logs shares all of the challenges of analyzing different community logs, the dealing with of those variations presents extra challenges.
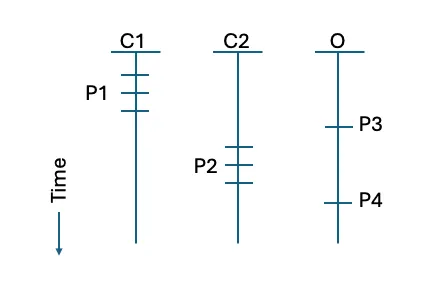
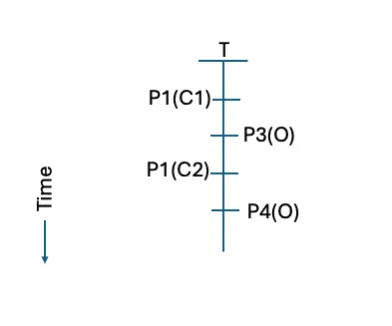
Determine 1: Instance set of timelines for an infrastructure applied throughout two CSPs (C1 and C2) and an on-premises host (O).
For example, contemplate Determine 1 above, which exhibits timelines for occasions throughout an infrastructure that’s applied throughout two CSPs and an on-premises internet hosting supplier. An analyst needs to judge the interactions, all of that are contacts from the identical exterior host as proven in Determine 1 by the small horizontal strains. Taking a look at every occasion or timeline individually, the contact seems non-threatening. By evaluating the interactions in combination, the analyst obtains a broader view of the exercise.
There are a number of potential methods of addressing variations between CSPs: current the outcomes individually, use separate analyses and caveat the outcomes, or interpolate the variations to restructure the information for a standard evaluation. Given the vary of selections out there, organizations looking for to enhance their entry and use of cloud circulation logs might architect an analytic infrastructure to swimsuit their wants. In any of those approaches, the general aim shall be to enhance consciousness of cloud exercise and to use that consciousness to enhance the safety of the group’s info.
The paragraphs under contemplate a number of approaches.
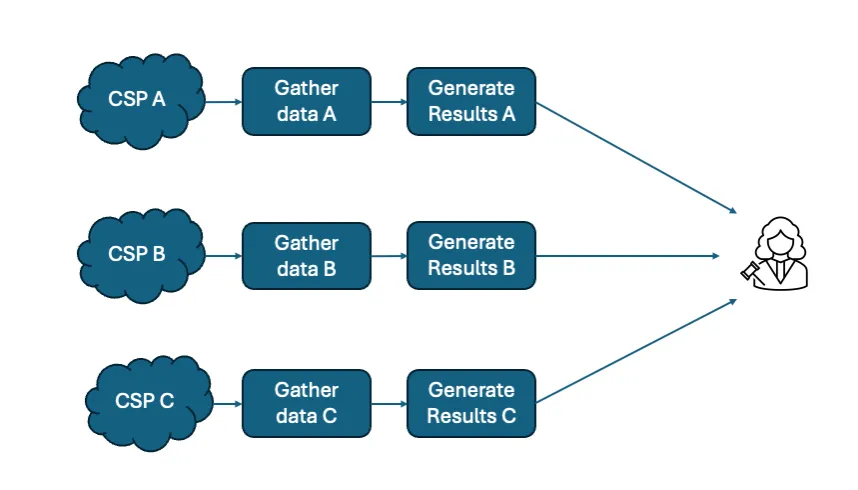
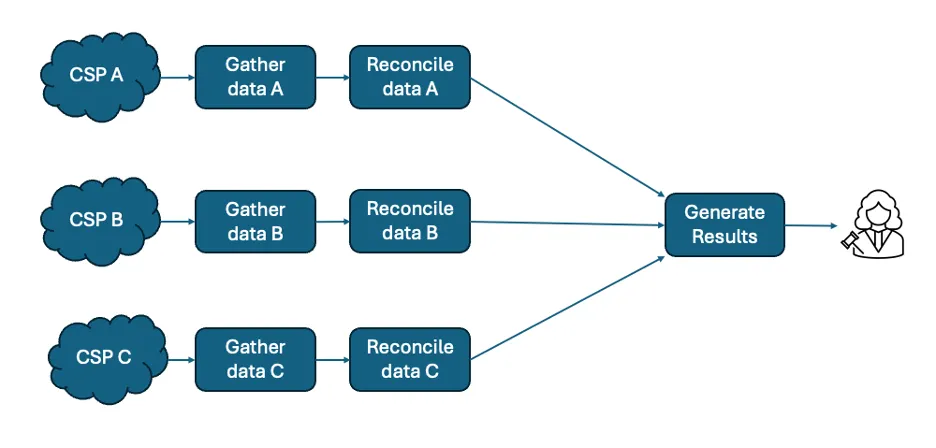
Determine 2: A separate outcomes evaluation strategy
The separate outcomes strategy proven in Determine 2 above makes use of every cloud’s information to generate a set of outcomes utilizing information buildings and evaluation strategies applicable to that cloud. Since separate suppliers produce logs, the setting of every supplier’s logs will differ.
Desk 1 under exhibits artificially-generated entries with the content material of logs from three cloud suppliers, simplified into tables and with chosen report fields for readability of show. Azure and Google logs are usually in JSON format, with Azure utilizing a deeply nested construction and Google a comparatively flat construction. AWS logs are usually in formatted textual content. The logs differ in that AWS (Desk 1c) and Google (Desk 1b) depict exercise as samples over time, whereas Azure (Desk 1a) describes exercise with start, proceed, and finish occasions at recognized instances.
Within the instance information in Desk 1, the Azure and AWS logs use IP addresses to discuss with cases, however the Google log makes use of occasion identifier strings. The separate outcomes strategy would go away these variations and never attempt to reconcile between them.
It’s obvious that the fields of the circulation information differ between suppliers, and the format of the person fields additionally differ, akin to for time values. There isn’t any clock synchronization throughout separate suppliers.
The separate outcomes strategy permits for essentially the most lodging to variations between clouds, with out contemplating the comparability of outcomes from different clouds. The separate outcomes strategy aligns with the particular CPS environments, however on the potential price of obscuring frequent actors or strategies that have an effect on multi-cloud internet hosting employed by a corporation.

Desk 1: Instance cloud circulation logs
Determine 3: An instance of the separate outcomes evaluation with 4 occasions (P1-P4)
In Determine 3, the analyst examines every CSP and the on-premises information individually. This produces a collection of 4 occasions (one in every of the cloud-hosted functionalities and two within the on-premises hosted performance). These occasions may be ordered, however the differing nature of the cloud information assortment prevents each exact time relationships and use of the main points recorded within the circulation report.
Utilizing this strategy does enable a broader view than the beforehand mentioned evaluation, however not the extent of element usually desired by the analyst. Nevertheless, for these analysts primarily centered on a single cloud implementation, the separate outcomes strategy could also be most popular for simplicity.
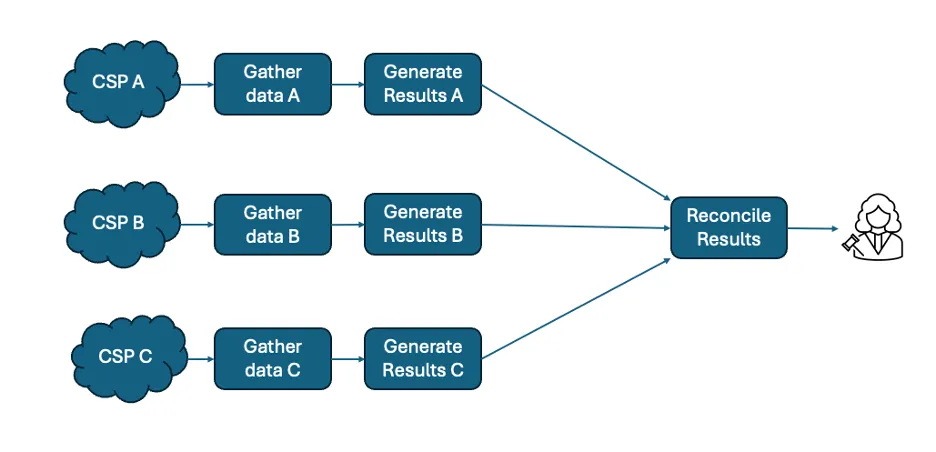
Determine 4: A separate evaluation strategy that features outcome reconciliation
An alternate technique is the separate evaluation strategy, which applies strategies focused to every CSP’s distinctive options however presents outcomes with format and content material that enable a reconciliation course of to supply a standard set of outcomes as proven in Determine 4. For instance, Every line of outcomes might normalize IP addresses to a standard format through the use of enrichment info, akin to registration or DNS decision. Every course of might reconcile timestamps by offsetting for clock skew and utilizing a shared format. This strategy permits for a standard consciousness throughout multi-cloud internet hosting, however potential prices embody sacrifice of the extra info {that a} single CSP might present and lack of precision in timing and quantity info to accommodate variations in assortment processes between clouds. The SEI has launched an open supply set of scripts implementing this strategy for AWS and for Azure.
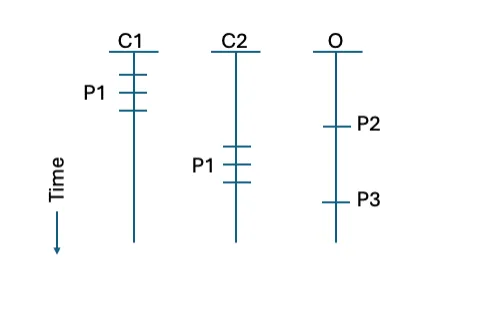
Determine 5: An instance of the separate evaluation strategy that results in sample identification
In Determine 5 above we see that making use of the separate evaluation strategy permits identification that the 2 occasions on the CSPs are each cases of the identical sample. Wanting on the information in Desk 1, the query-response construction of the interactions includes inspecting port and protocol pairing in Desk 1a however supply and vacation spot matching in Desk 1b. This requires separate evaluation logic to achieve a standard understanding. The same habits along with comparable packet and byte sizes in every of the 2 clouds helps identification of the exercise with a standard sample. This identification permits utility of the options of the sample within the evaluation, though clocks within the separate clouds will not be synchronized, which means the occasion ordering could also be inferred however not the time interval between occasions. Nevertheless, for comparatively low velocity assortment throughout a number of clouds, the separate evaluation strategy could also be most popular for the extent of element it helps.
Determine 6: An instance of the frequent evaluation strategy
A 3rd technique is the frequent evaluation strategy as proven in Determine 6 above. This works by translating every set of cloud logs right into a format and content material that’s achievable from every CSP’s circulation logs. This strategy permits extra code-efficient analytical work processes since solely a single evaluation script is required to look at all the logs within the frequent format, plus the transformation scripts from every CSP’s format to the frequent format. There’s a potential for lack of sure fields from every CSP’s format, particularly people who don’t have any frequent format equal. As well as, assortment right into a single location from a number of clouds will probably contain data-transfer prices to the group. organizations might want to outline and apply applicable entry restrictions for the logs in frequent format, based mostly on their info safety insurance policies
Determine 7: A typical timeline from a standard evaluation
Determine 7 continues the instance by making use of the frequent evaluation strategy to resolve variations in circulation aggregation to interpolate exercise into a standard timeline. One potential interpolation can be to common the quantity info into a standard time unit, then align time models between sources (assuming the sources have moderately aligned clocks, even when not absolutely synchronized). Changing the options of the circulation information into frequent format (e.g., JSON, CSV, and many others.), order of options, and resolving any information construction points will even facilitate the frequent evaluation. As soon as aligned and transformed, the analyst might both deliver the information into a standard repository or apply the evaluation individually in source-specific repositories after which combination the outcomes into a standard timeline.
This combination view affords the chance for a complete view throughout information sources however at the price of extra processing and imprecision as a result of alignment course of. For a extra summary view throughout a number of clouds and to make sure a standard view of the outcomes, the shared evaluation strategy could also be most popular.
Future Work in Cloud Movement Evaluation on the SEI
The work reported on this weblog submit is exploratory and on the proof-of-concept stage. Future efforts will apply these strategies in manufacturing and at a practical scale. As such, additional points with infrastructure and with the work reported right here will come up and be addressed.
This submit has outlined three approaches for evaluation of cloud circulation log entries. Over time, additional approaches might emerge and be utilized on this evaluation, together with approaches extra suited to streaming evaluation somewhat than retrospective evaluation.
Cloud circulation logs will not be the one operations-focused cloud information sources. CSP-specific sources, akin to cloudTrail and S3 logs might have entries that correlate with cloud circulation logs. Since these logs might present extra particulars on the purposes producing the visitors, they might present extra context to enhance safety. To facilitate this correlation, figuring out the baseline of exercise in these logs and evaluating it with the baseline in cloud circulation logs will tackle problems with scale.
Safety researchers have described malicious exercise via Techniques, Strategies, and Procedures (TTPs). A number of catalogs of such TTPs exist and analysts might map exercise in cloud circulation logs (and different information sources) to determine consistencies with TTPs. This might result in improved safety detection.
SEI researchers are working to develop the suitable construction for a multi-cloud repository of circulation log information. Given the price mannequin frequent amongst CSPs, such a repository will probably have to be a distributed construction, and that may contain problems within the question and response infrastructure.
Cloud information derived from a number of sources may be costly to retailer as a result of velocity of the information. Insurance policies must stability price towards worth of the information. This may be advanced since some analyses might require longer information retention intervals. There have been community assaults such because the Sunburst assault on SolarWinds) which have exploited log retention instances to hide their exercise. Some cloud information sources seem to have worth in reporting transient circumstances of relevance to safety. For instance, some service logs report inputs that fail to comply with anticipated formatting. This can be as a result of misconfigurations, transmission errors, or a type of vulnerability probing. Such log entries are unlikely to be of lasting worth in assessing safety since they report detected (and sure blocked) inputs. Different cloud information sources are more likely to be of extra lasting worth. An instance can be entries mapping to TTPs as described earlier. A course of is required to judge cloud information sources for long run retention versus people who ought to solely feed streaming anomaly detection, with out long run storage of entries.

