As organizations scale, managing entry permissions for storage sources turns into more and more complicated and time-consuming. As new workforce members be part of, current workers adjustments roles, and new S3 buckets are created, organizations should consistently replace a number of varieties of entry insurance policies to manipulate entry throughout their S3 buckets. This problem is particularly pronounced in multi-tenant S3 environments the place directors should steadily replace these insurance policies to regulate entry throughout shared datasets and quite a few customers.
At this time we’re introducing attribute-based entry management (ABAC) for Amazon Easy Storage Service (S3) basic function buckets, a brand new functionality you need to use to mechanically handle permissions for customers and roles by controlling information entry by tags on S3 basic function buckets. As an alternative of managing permissions individually, you need to use tag-based IAM or bucket insurance policies to mechanically grant or deny entry based mostly on tags between customers, roles, and S3 basic function buckets. Tag-based authorization makes it simple to grant S3 entry based mostly on undertaking, workforce, price heart, information classification, or different bucket attributes as a substitute of bucket names, dramatically simplifying permissions administration for giant organizations.
How ABAC works
Right here’s a standard situation: as an administrator, I need to give builders entry to all S3 buckets meant for use in growth environments.
With ABAC, I can tag my growth setting S3 buckets with a key-value pair similar to setting:growth after which connect an ABAC coverage to an AWS Id and Entry Administration (IAM) principal that checks for a similar setting:growth tag. If the bucket tag matches the situation within the coverage, the principal is granted entry.
Let’s see how this works.
Getting began
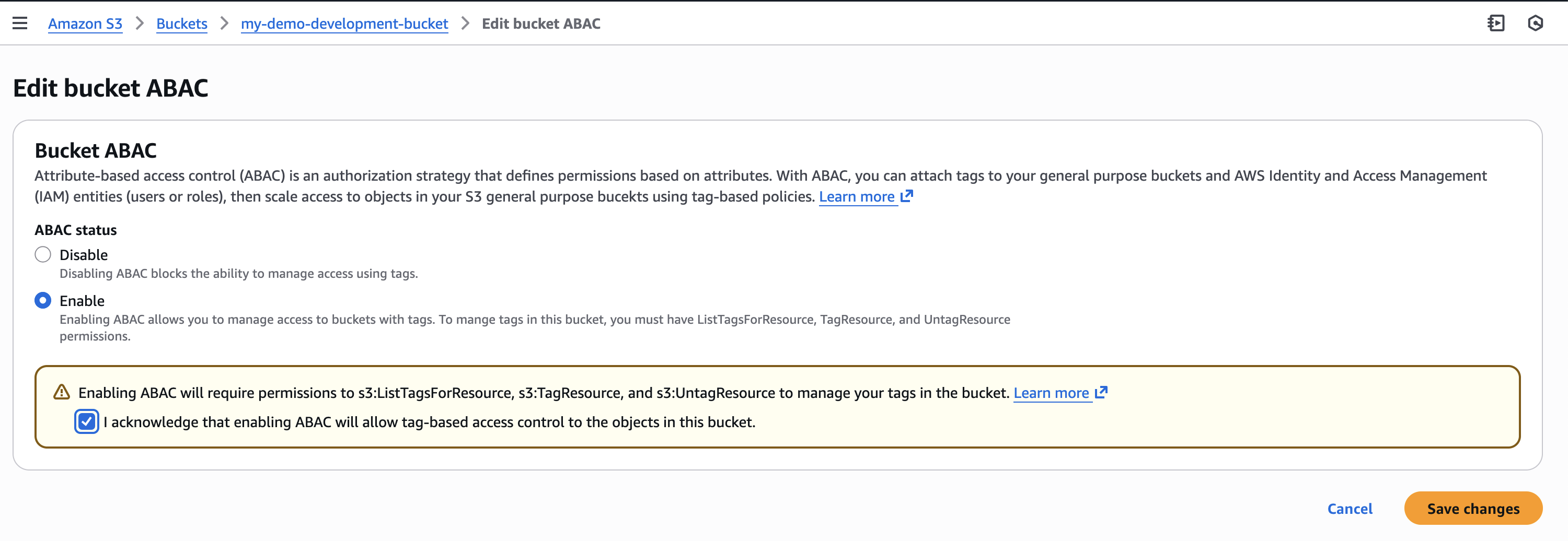
First, I have to explicitly allow ABAC on every S3 basic function bucket the place I need to use tag-based authorization.
I navigate to the Amazon S3 console, choose my basic function bucket then navigate to Properties the place I can discover the choice to allow ABAC for this bucket.
I also can use the AWS Command Line Interface (AWS CLI) to allow it programmatically by utilizing the brand new PutBucketAbac API. Right here I’m enabling ABAC on a bucket known as my-demo-development-bucket positioned within the US East (Ohio) us-east-2 AWS Area.
aws s3api put-bucket-abac --bucket my-demo-development-bucket abac-status Standing=Enabled --region us-east-2Alternatively, for those who use AWS CloudFormation, you possibly can allow ABAC by setting the AbacStatus property to Enabled in your template.
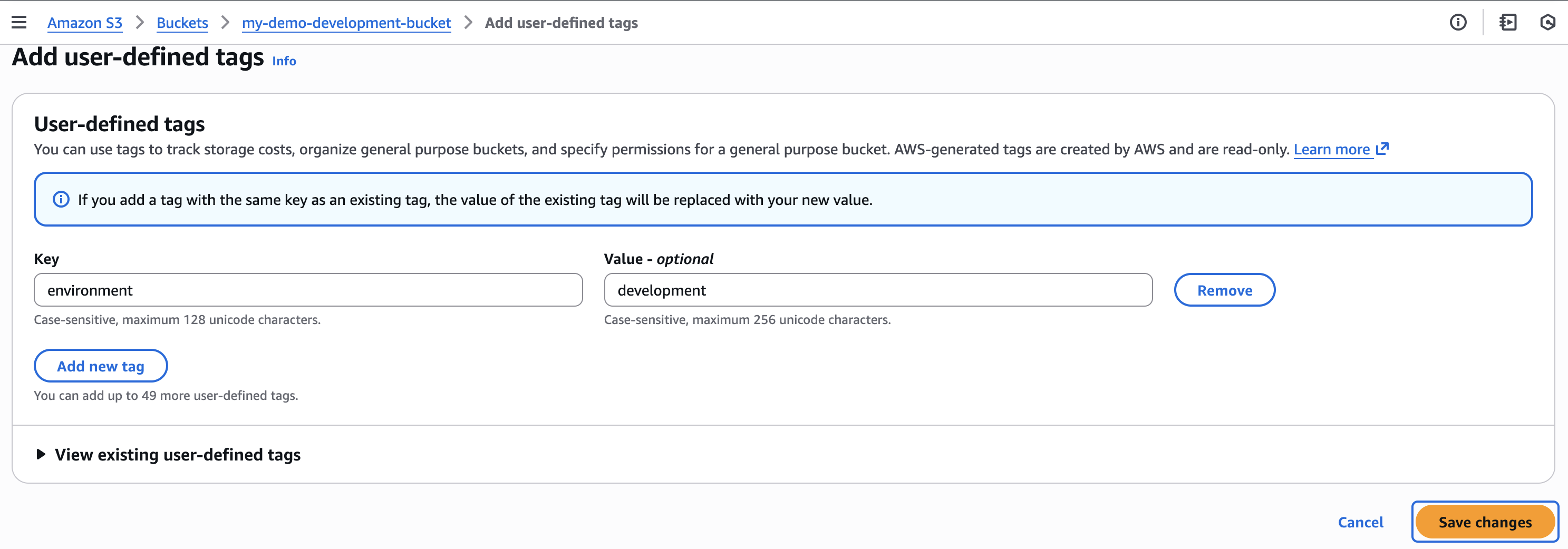
Subsequent, let’s tag our S3 basic function bucket. I add an setting:growth tag which can turn out to be the factors for my tag-based authorization.
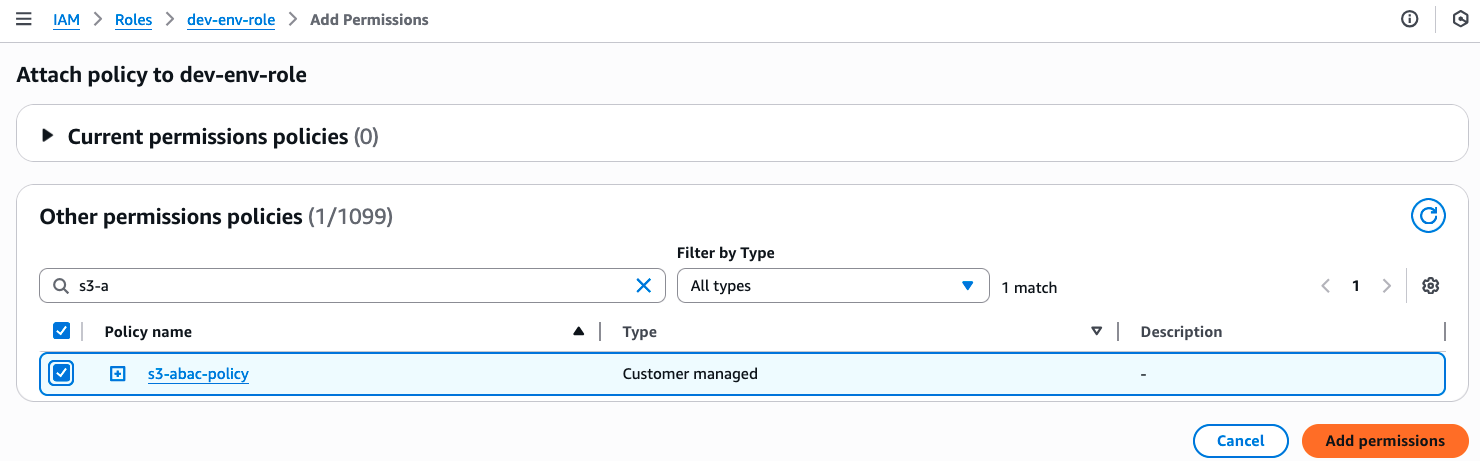
Now that my S3 bucket is tagged, I’ll create an ABAC coverage that verifies matching setting:growth tags and fasten it to an IAM function known as dev-env-role. By managing developer entry to this function, I can management permissions to all growth setting buckets in a single place.
I navigate to the IAM console, select Insurance policies, after which Create coverage. Within the Coverage editor, I swap to JSON view and create a coverage that permits customers to learn, write and record S3 objects, however solely after they have a tag with a key of “setting” connected and its worth matches the one declared on the S3 bucket. I give this coverage the identify of s3-abac-policy and put it aside.
{
"Model": "2012-10-17",
"Assertion": [
{
"Effect": "Allow",
"Action": [
"s3:GetObject",
"s3:PutObject",
"s3:ListBucket"
],
"Useful resource": [
"*"
],
"Situation": {
"StringEquals": {
"aws:ResourceTag/setting": "growth"
}
}
}
]
}I then connect this s3-abac-policy to the dev-env-role.
That’s it! Now a person assuming the dev-role can entry any ABAC-enabled bucket with the tag setting:growth similar to my-demo-development-bucket.
Utilizing your current tags
Needless to say though you need to use your current tags for ABAC, as a result of these tags will now be used for entry management, we suggest reviewing your present tag setup earlier than enabling the characteristic. This consists of reviewing your current bucket tags and tag-based insurance policies to stop unintended entry, and updating your tagging workflows to make use of the usual TagResource API (since enabling ABAC in your buckets will block the usage of the PutBucketTagging API). You should utilize AWS Config to verify which buckets have ABAC enabled and overview your utilization of PutBucketTagging API in your software utilizing AWS Cloudtrail administration occasions.
Moreover, the identical tags you utilize for ABAC also can function price allocation tags on your S3 buckets. Activate them as price allocation tags within the AWS Billing Console or by APIs, and your AWS Value Explorer and Value and Utilization Stories will mechanically arrange spending information based mostly on these tags.
Implementing tags on creation
To assist standardize entry management throughout your group, now you can implement tagging necessities when buckets are created by service management insurance policies (SCPs) or IAM insurance policies utilizing the aws:TagKeys and aws:RequestTag situation keys. Then you possibly can allow ABAC on these buckets to offer constant entry management patterns throughout your group. To tag a bucket throughout creation you possibly can add the tags to your CloudFormation templates or present them within the request physique of your name to the present S3 CreateBucket API. For instance, I might implement a coverage for my builders to create buckets with the tag setting=growth so all my buckets are tagged precisely for price allocation. If I need to use the identical tags for entry management, I can then allow ABAC for these buckets.
Issues to know
With ABAC for Amazon S3, now you can implement scalable, tag-based entry management throughout your S3 buckets. This characteristic makes writing entry management insurance policies less complicated, and reduces the necessity for coverage updates as principals and sources come and go. This helps you cut back administrative overhead whereas sustaining sturdy safety governance as you scale.
Attribute-based entry management for Amazon S3 basic function buckets is on the market now by the AWS Administration Console, API, AWS SDKs, AWS CLI, and AWS CloudFormation at no further price. Commonplace API request charges apply in response to Amazon S3 pricing. There’s no further cost for tag storage on S3 sources.
You should utilize AWS CloudTrail to audit entry requests and perceive which insurance policies granted or denied entry to your sources.
You may also use ABAC with different S3 sources similar to S3 listing bucket, S3 entry factors and S3 tables buckets and tables. To study extra about ABAC on S3 buckets see the Amazon S3 Consumer Information.
You should utilize the identical tags you utilize for entry management for price allocation as nicely. You possibly can activate them as price allocation tags by the AWS Billing Console or APIs. Try the documentation for extra particulars on use price allocation tags.