From early 2022 via late 2024, a bunch of risk actors publicly generally known as APT28 exploited identified vulnerabilities, equivalent to CVE-2022-38028, to remotely and wirelessly entry delicate info from a focused firm community. The assault first compromised much less safe Wi-Fi networks of a number of organizations that have been in shut bodily proximity to the meant goal. This incident brings to gentle the important position that software program performs within the safety of modern-day wi-fi communication techniques, each army and civilian. This assault didn’t require any {hardware} to be positioned within the neighborhood of the focused firm’s community because the attackers have been in a position to execute remotely from hundreds of miles away.
With the ubiquity of Wi-Fi, mobile networks, and Web of Issues (IoT) units, the assault floor of communications-related vulnerabilities that may compromise knowledge is extraordinarily giant and continuously increasing. Anybody who holds knowledge in digital type—from private info to company mental property to nationwide safety info—ought to concentrate on the roles of software program and cybersecurity in wi-fi techniques and tips on how to shield towards software-based assaults.
On this weblog publish, we evaluate widespread radio frequency (RF) assaults and examine how software program and cybersecurity play key roles in these exploitations. We begin with an summary of the Open System Interconnection (OSI) mannequin. Then we are going to delve into safety features of contemporary wi-fi communication techniques with examples of vulnerabilities, exploitations, weaknesses, and the way these may impression the wi-fi system. We’ll conclude with software program and safety mitigations.
Overview of the OSI Stack
The idea of layering is a type of purposeful modularity that’s helpful in communication techniques. The motivation of a layered method is to decompose a posh design downside into extra manageable ones and facilitate standardization. Much like knowledge representations in computing, a pure layering exists in wi-fi communication networks. Broadly talking, the bottom layers relate to the physics of connectivity (i.e., wi-fi, copper wire, fiber optical, and so forth). Layered on prime of this are encodings to help the illustration of binary bits and their meeting into binary strings. Above this are layers that relate to the switch of binary strings. Above these are layers that give application-specific meanings to the binary strings. Assault surfaces and potential vulnerabilities exist at each degree. As we discover layers of the OSI mannequin all through this part, we additionally have a look at a number of examples of potential software-enabled assaults at every layer.
The Worldwide Group for Standardization (ISO) defines the OSI mannequin as “a standard foundation for the coordination of requirements growth for the aim of techniques interconnection.” Whereas the OSI stack is relevant to each bodily wired and wi-fi networks, this weblog publish will deal with the layers of the stack from the wi-fi communication perspective. The OSI mannequin is a really extensively adopted scheme used to explain and handle the layering. The underside three layers (Bodily, Information Hyperlink, and Community) signify {hardware} features of connectivity. The Transport Layer serves because the central mechanism for controlling knowledge switch. As proven in Determine 1 beneath, the highest three layers (Session, Presentation, and Utility) are sometimes referenced because the software program layers; nonetheless, you will need to be aware that in trendy wi-fi communication techniques, software program is prevalent in all seven layers of the OSI mannequin stack.
Determine 1: Abstract of OSI Layers derived from Stallings
Bodily Layer
The Bodily Layer, additionally known as the PHY or layer 1, is the bottom layer of the OSI stack and addresses interactions of {hardware}, transmission, and signaling mechanisms. In trendy wi-fi techniques, the PHY is usually supported utilizing digital, analog, and/or mixed-signal RF chips, in addition to a digital baseband chip for digital sign processing (DSP) and communication algorithm processing equivalent to channel coding. Channel coding strategies, equivalent to Ahead Error Correction (FEC), are employed in digital communications and add managed redundancy to knowledge to detect and proper errors launched by interference or noise on the communication channel. On the transmitter, the encoder provides redundant bits to the unique knowledge that will likely be despatched. On the receiver, the decoder will use these redundant bits to establish and proper errors. We’ll go into larger element about error detection and correction within the Information Hyperlink Layer part beneath.
Within the context of wi-fi communication techniques, the PHY layer is liable for sending and receiving radio frequency indicators. The PHY defines the strategies for transmitting uncooked bits over a wi-fi knowledge hyperlink connecting community nodes and units. The PHY interfaces with the Information Hyperlink Layer, which arms over the info within the type of bits that will likely be transmitted by the PHY. The PHY layer additionally manages the transition between processing the bitstream within the computational digital realm to the frequencies and emissions which can be the RF realm. A typical model of a binary numerical definition of a waveform will get transformed right into a radiating electromagnetic wave (RF wave) within the PHY. Versus a wired community, no specific bodily medium is required; nonetheless, RF propagation traits differ primarily based on the setting of the wi-fi transmission. A selected RF sign transmitted at a specific frequency in a specific setting is named a channel. Relying on the system, a single channel or simultaneous a number of channels could also be used. The PHY of the receiving machine captures the radiated modulated RF sign and converts it again into time-sampled digital binary numbers representing the uncooked transmitted sign, together with potential noise and errors inherited from the shared setting of the channel. For many wi-fi techniques, body synchronization happens on the PHY after demodulation and ensures alignment of the receiver clocks with corresponding transmitter clocks. Body synchronization specifies how a receiver identifies the beginning and finish of knowledge frames within the obtained bitstream by finding a singular synchronization sample, equivalent to a preamble, embedded at first of every body.
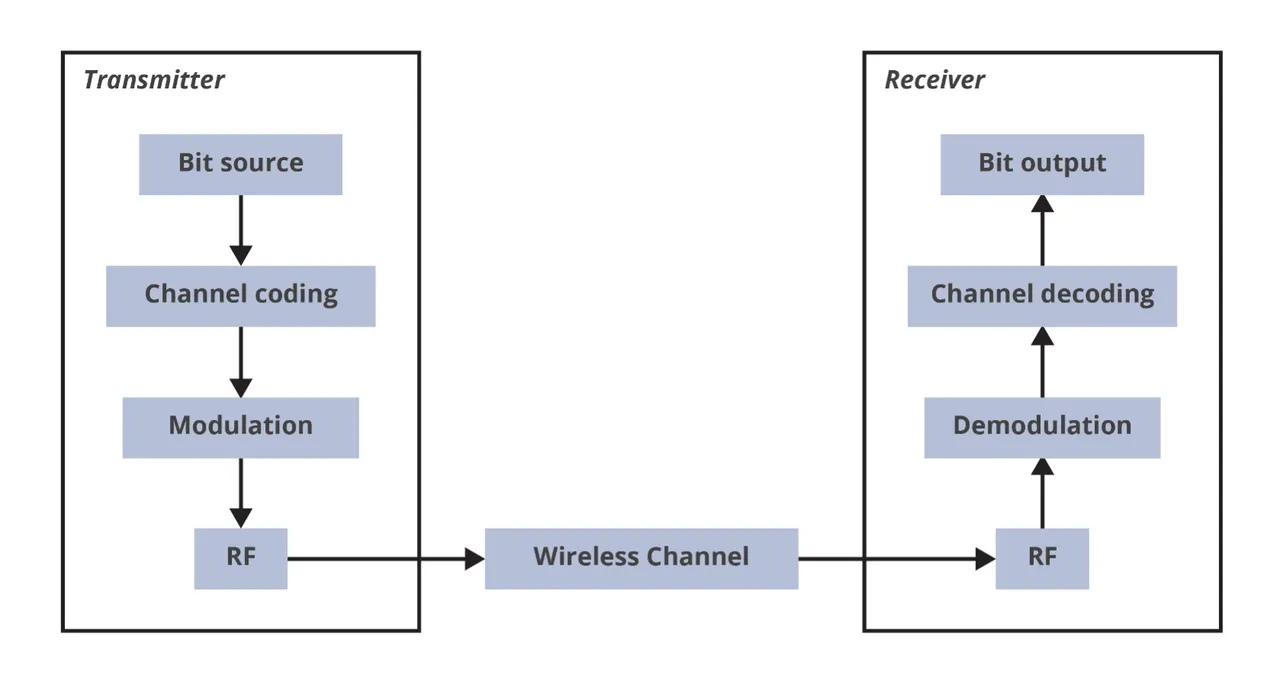
The bits are additional organized and processed within the Information Hyperlink Layer. Determine 2 depicts a generalized Bodily Layer structure of a transmitter and receiver pair. The PHY considerations point-to-point or point-to-multipoint (i.e., broadcast) connections, versus multi-hop networks, equivalent to wi-fi mesh networks, which is the priority of higher layers within the OSI stack.
On the PHY Layer, an instance of a software-enabled assault vector is knowledge contamination, through sign sniffing. In one of these assault, the attacker broadcasts a sign that’s stronger (i.e., greater energy) than the official and meant sign and is falsified to deprave the official communications hyperlink. This stronger, falsified sign on the bodily layer could be employed such that the software program within the wi-fi community that handles machine connection and site visitors routing is tricked into rerouting site visitors to the attacker. An attacker may additionally disrupt or deny wi-fi communications by concentrating on synchronization indicators to disrupt body synchronization. Jamming assaults equivalent to synchronization sign jamming and burst jamming intention to override or trick the official synchronization indicators of a wi-fi system. One other method is to spoof or manipulate indicators to mislead the receiver. For instance, an attacker may inject right into a Wi-Fi community solid preambles that precede the precise knowledge body. By spoofing the preamble on this approach, the assault can power units to attend for the expiration of an introduced knowledge body period, successfully silencing the channel. In one other assault method, the risk actor may spoof the well-known time synchronization normal of a World Navigation Satellite tv for pc System (GNSS), equivalent to GPS. This assault broadcasts counterfeit GNSS indicators at a better energy degree than official satellite tv for pc indicators inflicting the goal receiver synchronization and monitoring to lock onto the faux sign. This might enable the attacker to govern the focused machine’s notion of time or location disrupting or denying its capacity to obtain and decode knowledge.
Information Hyperlink Layer
Layer 2 of the OSI mannequin stack, the Information Hyperlink Layer (DLL), manages bodily addressing (versus community addressing) and entry management to the PHY to detect and/or stop knowledge collisions in a channel. The DLL additionally handles error correction, knowledge stream management, and the reassurance of dependable knowledge body switch throughout the wi-fi channel. On a typical wi-fi community, equivalent to these outlined by IEEE802, this layer is split into two sublayers: Logical Hyperlink Management (LLC) and the Media Entry Management (MAC). Each related machine is supposed to have a singular MAC handle, which is 48 bits lengthy for IEEE 802 MAC addresses however could possibly be totally different lengths for different requirements. The DLL-MAC layer makes use of these distinctive addresses to handle how units acquire entry to the community utilizing protocols. The MAC handle can also be utilized to establish meant recipients of the info frames.
Error detection and correction can also be dealt with within the Information Hyperlink Layer. Error-correcting codes can be utilized to enhance the efficiency of a digital communication system. The everyday measure of efficiency is the bit error charge (BER) versus vitality per bit to noise density ratio (Eb/No). The BER is the likelihood of the reception of an incorrect bit. Within the easy instance proven in Determine 3, we see that the twelfth bit within the stream (highlighted in blue) despatched from a transmitter (Tx) was obtained incorrectly on the receiver (Rx). By including managed redundancy to the info on the transmitter earlier than sending to the receiver, lack of knowledge (bits) because of interference or noise encountered on the channel could be detected on the receiver and reconstructed to forestall the lack of info within the transmission. The DLL additionally handles the speed of knowledge switch (knowledge stream) to forestall the transmitter from overwhelming the receiver(s) by sending an excessive amount of knowledge or sending knowledge too shortly.

Determine 3: Easy Bit Error Instance
The Information Hyperlink Layer is inclined to software-enabled assault vectors together with faux entry level nodes, MAC handle spoofing, and Wi-fi Native Space Community (WLAN) driver assaults.
In a faux entry level assault, often known as an evil twin, the attacker establishes a malicious entry level (AP) with the identical Service Set Identifier (SSID) because the official AP to trick person units into connecting to a faux community. As soon as a tool is related to this faux community, the attacker can execute a person-in-the-middle assault to seize the machine’s wi-fi community site visitors and the info being despatched and obtained.
MAC spoofing happens when an attacker modifications a tool’s MAC handle to impersonate one other official machine on the wi-fi community. This can be utilized to bypass MAC handle filtering that could be in place or to execute different kinds of community assaults.
To conduct a WLAN driver assault, the risk actor exploits software program vulnerabilities within the wi-fi community card drivers of a related machine. These exploitations can expose routes to the attackers on which they’ll execute malicious code and acquire management over wi-fi community or system.
Community Layer
The third layer is the Community Layer, which handles inter-network connections together with managing routes for knowledge packets, pinging servers in different networks to verify availability, and addressing and receiving packets from different networks. Routing determines the perfect path for knowledge packets to journey from a supply to a vacation spot, even throughout a number of networks, by utilizing routing protocols and algorithms. Packet forwarding strikes knowledge packets from one community to a different primarily based on routing selections, connecting totally different networks.
In a multi-node wi-fi community, knowledge/communication packets are moved throughout the community from node to node, which is known as hopping. Whereas wired networks extra generally have static routes because of the bodily wiring between nodes, wi-fi routing could be both static or dynamic in nature. A wi-fi mesh community (WMN) is usually comprised of finish node units/purchasers mixed with routes and gateways. If the mobility of mesh purchasers is minimal, the community topology tends to be largely static. Usually WMNs depend on static nodes to operate as gateways and, on this approach, they’re just like wired networks. By comparability, a decentralized cell advert hoc community (MANET), is designed to not depend on pre-existing or mounted infrastructure equivalent to routers, gateways, or wi-fi entry factors. Reasonably, every MANET node actively participates in site visitors routing by relaying knowledge for different nodes within the community. The choice of which nodes ahead knowledge is executed dynamically primarily based on community connectivity and the community’s routing algorithm. Because of the dynamic nature of the routing, every node within the MANET can transfer independently of the opposite nodes, and the hyperlinks to different units could also be up to date steadily.
Packet sniffing or capturing and observing over-the-air knowledge packets, is an instance of a Community Layer software-enabled assault vector. Because of the over-the-air broadcast nature of wi-fi indicators, an attacker can passively seize packets from the community and probably collect info or intercept delicate site visitors, even beneath encryption layer. From this info, the attacker could possibly decide the sample of lifetime of the sign (i.e., how typically it transmits, energy ranges, frequencies, and so on.). For example, packet sniffing and capturing knowledge could be detrimental to the decentralized MANET beforehand mentioned. To ascertain and keep environment friendly and dynamic community routing in a MANET, metadata about every node needs to be continuously despatched to different nodes throughout the community. This creates potential info leakage if this metadata is captured through packet sniffing. As soon as an attacker has captured info associated to the MANET message routing, they can exploit vulnerabilities by focusing assaults on the routing algorithms, by isolating focused nodes from the community, or by inserting a false node on the community with malicious intent.
Transport Layer
The Transport Layer (TL), or layer 4, resides above the Community Layer and is liable for guaranteeing knowledge packets arrive reliably and precisely between purposes working on units throughout the community. The transmitter TL accomplishes this by breaking giant knowledge streams into smaller, manageable segments, and the receiver TL reassembles these segments. On the TL, the most typical protocols utilized to alternate messages over a community are the Transmission Management Protocol (TCP) and the Consumer Datagram Protocol (UDP). TCP is usually used for knowledge streams which can be extremely dependable and should be absolutely and precisely communicated on the potential value of latency. UDP can be utilized for decrease latency knowledge streams the place the worth of a missed packet may need a negligible impact, equivalent to media streams and real-time knowledge transmission. As soon as the packets and segments have been reassembled, they’re pushed as much as the Session Layer for the corresponding program/software on the top machine. Whereas TCP and UDP are designed to work on each wired and wi-fi networks, wi-fi variations additionally embrace extra safety layers such because the Wi-fi Transport Layer Safety (WTLS) to guard knowledge. This extra layer of safety is just not usually required on the similar degree of safety in wired networks the place bodily entry is a barrier to ingress. In wi-fi networks, the Transport Layer might also require extra aggressive error management strategies than wired networks because of the greater probability of packet loss and corruption primarily based on interference.
TCP hijacking is a standard software-enabled assault within the Transport Layer of the OSI mannequin stack. TC/IP hijack assaults intercept and take management of the TCP session established between two wi-fi units on a community by predicting or capturing the sequence numbers used to synchronize and manage official connection and interplay. With management of the TCP/IP session, the attacker can take over a person session by stealing or predicting the session token. This permits official person impersonation, entry to delicate knowledge, and skill to execute unauthorized actions on the machine or community.
Session Layer
Layer 5 within the OSI mannequin stack is the Session Layer. In a wi-fi system, the Wi-fi Session Protocol (WSP) implements the Session Layer performance and is liable for the institution, upkeep, and termination of communication classes between related units on the wi-fi community. The WSP may also handle the allocation and subsequent launch of community sources in the course of the established session.
In an identical method to the hijacking mentioned within the earlier part, session fixation assaults are an instance of Session Layer software-enabled assaults. In a session fixation assault, the risk actor forces a certified person’s session ID to a predictable worth then, as soon as the person gives authentication info, the attacker can use the identical ID to hijack that session with related outcomes to the earlier layer.
Presentation Layer
The Presentation Layer, the sixth layer of the OSI mannequin stack, is liable for making ready knowledge for the receiving software on the machine. This layer handles duties equivalent to knowledge translation, compression, and encryption (though encryption may also be accomplished at different layers as nicely). In wi-fi techniques, this layer is essential in guaranteeing interoperability between totally different units and techniques, particularly when these units might make the most of differing knowledge codecs or encoding strategies. Information translation converts knowledge between totally different codecs, for instance Unicode or its predecessor, the American Normal Code for Data Interchange (ASCII). Unicode applied a dramatic growth from ASCII’s unique 7-bit encoding of characters to codecs of 8, 16, or 32 bits, permitting for very giant character units. There are additionally legacy codecs equivalent to Prolonged Binary Coded Decimal Interchange Code (EBCDIC), nonetheless used on some mainframe computer systems. Information compression is employed to enhance effectivity and latency by decreasing the quantity of data that’s transmitted over the community. Encryption may also be accomplished on the Presentation Layer, permitting for confidentiality and safety of the info. The transmitter encrypts the info earlier than transmission, and it’s decrypted upon reception on the receiver node.
On the Presentation Layer, a buffer overflow assault exploits software program vulnerabilities within the areas the place a program writes knowledge to a reminiscence buffer that isn’t sufficiently giant sufficient to carry all of the written knowledge. This extra knowledge “overflows” the goal reminiscence buffer to overwrite adjoining reminiscence areas which could be manipulated by an attacker to trigger this system to crash, leak info, or execute arbitrary or malicious code. The malicious code can execute with the identical degree of privileges because the weak software, probably granting full entry to the system. Overflowing the buffer can even corrupt vital knowledge or expose delicate info saved in adjoining reminiscence. Encryption implementation flaws within the Presentation Layer may additionally expose a vector for assaults. Exploitation of weak or improperly applied encryption protocols can enable unintended decryption and entry to delicate knowledge.
Utility Layer
The seventh and highest layer within the OSI mannequin stack is the Utility Layer. This layer serves because the interface between the top person and purposes to entry the wi-fi community companies. The Utility Layer handles duties equivalent to e mail companies and protocols utilized for net shopping together with the Easy Mail Switch Protocol (SMTP) and Hypertext Switch Protocol (HTTP). This layer ensures {that a} given software can successfully talk with different purposes on totally different units and networks. Nonetheless, you will need to be aware that the Utility Layer is just not an software itself.
Provided that the Utility Layer is nearly fully composed of software program, there are lots of assault vectors and vulnerabilities that may be exploited. Particular examples embrace Structured Question Language (SQL) injection, Cross-Website Scripting, and Border Gateway Protocol (BGP) hijacking.
SQL is a domain-specific language used for database administration techniques. In an SQL injection assault, malicious SQL code is injected into the enter fields of the goal software, probably resulting in unauthorized entry, knowledge theft, or knowledge corruption.
Cross-site scripting employs malicious software program scripts which can be injected into net purposes which can be then executed by a person’s net browser, typically with out their information. Execution of those malicious cross-site scripts can result in session hijack, as beforehand mentioned, or to unauthorized knowledge exfiltration.
In a BGP hijack assault, the attacker misrepresents possession of a goal web site’s IP handle to maliciously reroute incoming and outgoing site visitors, permitting for the interception or manipulation of knowledge.
Software program Implications for Safety of Wi-fi Communications System
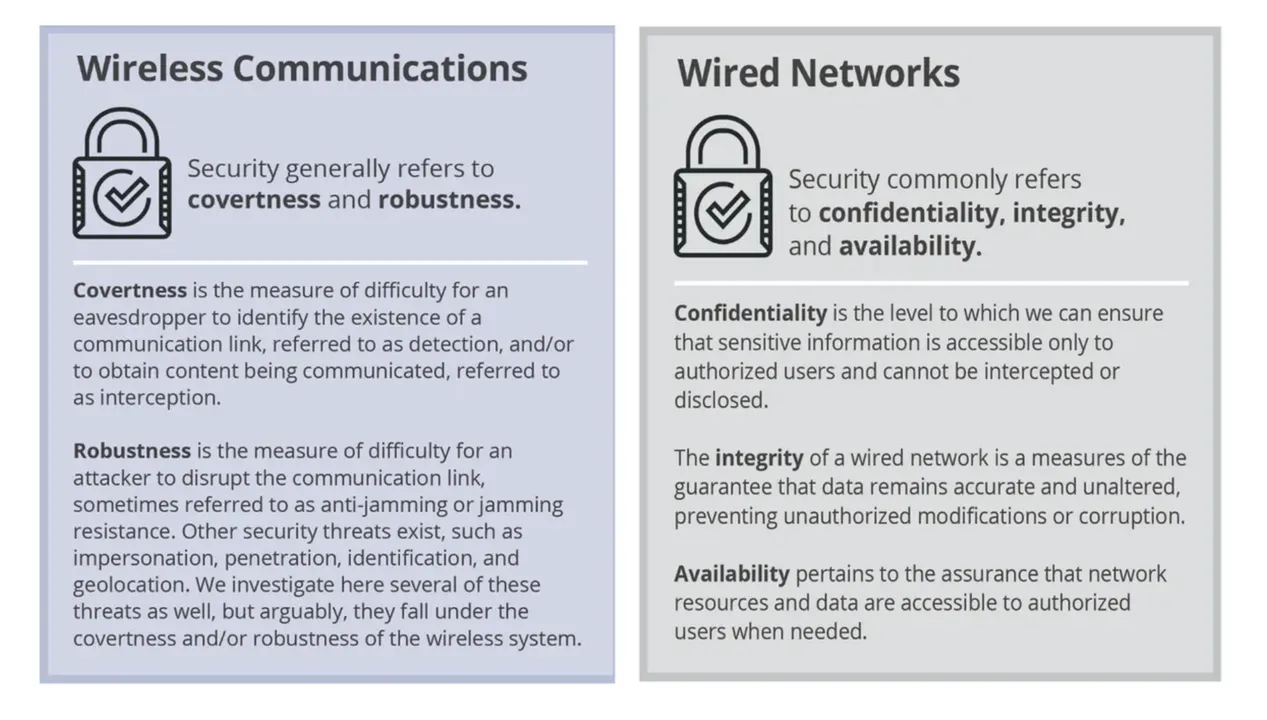
Determine 4: Contrasting Wi-fi and Wired Community Safety
From the safety and knowledge safety perspective, you will need to distinction a number of traits of wired versus wi-fi networks. Determine 4 gives as fast abstract of how safety is usually outlined for each kinds of networks. Each communication networks must do channel coding and sign processing, nonetheless the approaches and strategies must be basically totally different. For instance, in a wired Gigabit Ethernet connection, the standard of the copper wire and winding strategies within the Ethernet wire decide how channel coding and sign processing on the community could be accomplished. Essentially the most cheap approach for an attacker to intercept and exfiltrate knowledge is to bodily entry (faucet) the wire. This can be a substantial distinction to wi-fi networks the place the channel and sign is probably extra publicly out there because of the over-the-air, wi-fi nature of the hyperlinks and connections. Within the wi-fi case, the implementation must have robustness integrated within the design of the sign and connection to hinder unintentional or malicious interception and exploitation. Desk 1 summarizes similarities and variations between wi-fi and wired networks with respect to the OSI mannequin layers.
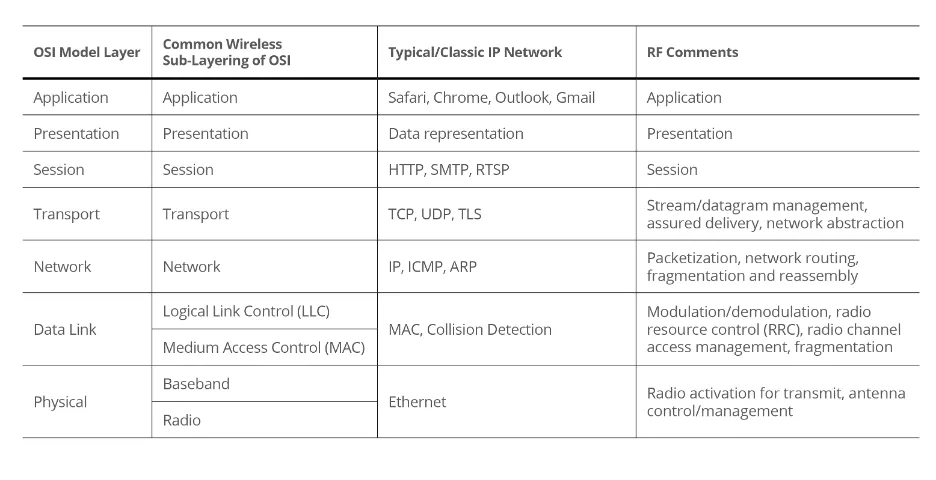
Desk 1: Abstract Comparability of Wi-fi and Wired OSI Mannequin Layers
Software program performs many important roles in trendy implementation of each wired and wi-fi communication techniques. With respect to wi-fi techniques, the position of software program within the prime three layers (Session, Presentation, and Utility) must be apparent; nonetheless, what could also be much less discernible is the position of software program within the {hardware} layers of the OSI stack (PHY, DLL, and Community). As beforehand mentioned, the PHY layer is primarily targeted on {hardware}. Nonetheless, with the rise of software-defined radios, software program is changing into extra prevalent on the decrease layers of the OSI stack as nicely. A software-defined radio (SDR) is a radio communication machine or system that implements conventional radio {hardware} elements (e.g., filters, mixers, modulators/demodulators, amplifiers, and so on.), both on a pc or as a part of an embedded system. Determine 4 beneath reveals a simplified illustration of the SDR idea for a radio receiver. The highest picture reveals a typical analog receiver comprised of conventional {hardware} elements, and the underside picture reveals a SDR receiver with elements applied in software program.
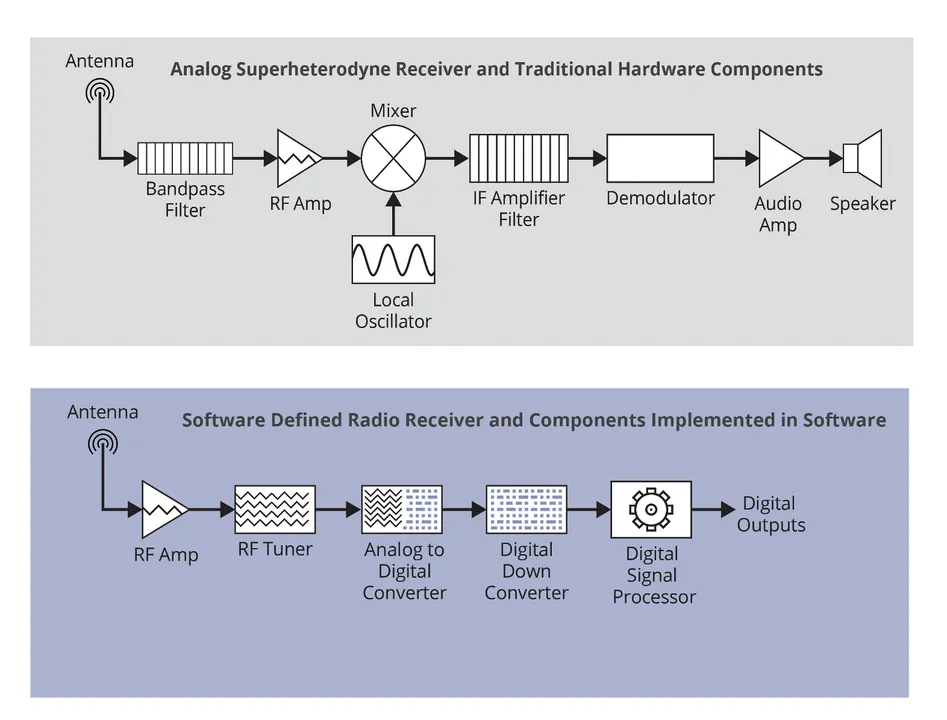
Determine 5: Prime: Analog Receiver with {Hardware} Elements; Backside: SDR Receiver with Software program Applied Elements
One of many key benefits of SDR is the usage of software program, which allows agile reprogrammability and reconfiguration, permitting for elevated flexibility and improved efficiency. This permits the person to change performance by downloading and working new software program at will. It additionally facilitates speedy prototyping workouts. Vital parts of the sign processing are dealt with by a general-purpose processor reasonably than special-purpose analog {hardware} (e.g., tubes, transistors, chips, and digital circuits).
Usually SDRs are full-duplex, which suggests they permit a single machine to each transmit and obtain concurrently. The usage of software program makes it potential for a single SDR to help a wide range of protocols and/or waveforms. As well as, an onboard field-programmable gate array (FPGA) can be utilized to encode/decode knowledge from a wide range of wi-fi requirements in addition to to encrypt or scramble knowledge earlier than transmission. These items may also be accomplished instantly in software program; nonetheless, this method usually requires a tradeoff in pace and latency. The flexibility to fulfill communication timing necessities, particularly with quick turnaround, can’t be simply accomplished in a general-purpose course of, nonetheless it’s potential to create larger flexibility within the protocol to permit for latencies within the general-purpose processor method. Alternatively, the system can make use of an FPGA or Utility Particular Built-in Circuit (ASIC) to cut back the timing overhead and get extra environment friendly use of the RF spectrum.
These configurations supply new sorts of vulnerabilities. For instance, malicious software program can be utilized to have an effect on or reprogram an FPGA to change the habits of a wi-fi communication system. A compromised FPGA may allow attackers to switch configurations or performance to disrupt, degrade, or usurp wi-fi communication techniques. For instance, attackers may reconfigure an FPGA to intercept and manipulate knowledge transmitted over wi-fi hyperlinks, jam official communication indicators, inject false info into the community site visitors, or exploit vulnerabilities in adjoining units or networks.
In a earlier weblog, RF 101: Can You Actually Hack a Radio Sign?, we reviewed a number of of the most typical kinds of RF assaults that may be employed to take advantage of vulnerabilities and intercept, disrupt, or manipulate wi-fi communication techniques and related protocols. Right here we revisit a number of of those RF assaults, in addition to some new ideas, to analyze how software program and cybersecurity play key roles in these exploitations.
Replay Assault
Replay assaults happen when a sound transmission is captured and retransmitted to impersonate a official machine or person. This assault exploits vulnerabilities in the best way that software program techniques deal with knowledge transmission, authentication, and authorization. Delicate knowledge that is likely to be captured can embrace session tokens or login credentials. Determine 5 depicts an instance of a fundamental replay assault. The attacker captures a sound authentication message despatched by a official person after which retransmits that message at a later time to realize entry to the community.

Determine 6: Replay Assault
An instance of a replay assault is discovered within the safety flaws of the Wi-Fi Protected Setup (WPS), a function designed to simplify the strategies of connecting units to current Wi-Fi networks through configuration potentialities equivalent to push-button or PIN-code entry. As soon as initiated, the push-button methodology depends on the person to push a button on each the shopper machine and the Wi-Fi router concurrently inside a set timeframe. An attacker may intercept and retransmit (replay) the official shopper machine’s indicators, tricking the router into accepting an unauthorized connection.
From a software program and cybersecurity perspective, there are a number of key strategies that may be employed to mitigate these exploitations. One step is to enhance software program authorization strategies by utilizing role- or attribute-based entry controls, which restrict person permissions, entry to info, and degree of interplay with the system primarily based on their person position or person profile attributes. Different mitigation steps embrace implementing least privilege to customers, denying entry by default, validating or re-validating permissions on each entry request, encrypting delicate knowledge, and implementing sturdy password insurance policies.
Relay Assault
A relay assault happens when the attacker serves as an middleman by intercepting and relaying communications between the transmitter and meant receiver with out explicitly manipulating the messages. A relay assault in a wi-fi community is analogous to a person-in-the-middle assault for a wired community and is typically referred to this manner in a wi-fi community as nicely. This sort of assault can be utilized to realize entry to techniques or companies or to bypass safety measures which can be in place. With out correct validation of the origin of communications, software program purposes and protocols counting on authentication and encryption could be exploited by relay assaults. Determine 6 reveals an instance of a relay assault by means of an intercepted and transferred key fob used to unlock a automobile. On this instance, one particular person may intercept to key fob sign, which is at all times transmitting, and relay the sign to a second particular person that’s near the automobile thus bypassing the necessity for the important thing fob to be in shut proximity to the automobile to unlock it. Equally, the sign to start out the automobile may also be captured and relayed to the second particular person.

Determine 7: Relay Assault
Just like the Wi-Fi replay assault mentioned within the earlier part, an attacker may make the most of a relay assault to realize unauthorized entry to Wi-Fi community. On this case, the attacker may use units, equivalent to an SDR, to relay the push-button indicators between the official shopper machine and the router, thus bypassing bodily proximity necessities.
Whereas there are some bodily mitigation approaches within the utilization of bodily safety keys (e.g., YubiKey), software program safety has an vital position as nicely. Sturdy authentication strategies, equivalent to multi-factor authentication (MFA), metric verification, and one-time passcodes, may also help to mitigate exploitations from relay assaults. Nonetheless, a few of these bodily mitigation approaches nonetheless require wi-fi communications that may be spoofed. For instance, attackers could possibly intercept after which ship a false passcode to a mobile phone or spoof the important thing exchanges on a wi-fi multi-factor authentication machine.
The APT28 nearest neighbor assault introduced within the introduction is a wonderful instance of the flexibility to sidestep MFA units. APT28 have been in a position to make the most of brute power password-spray assaults to acquire legitimate credentials to entry the goal community. Nonetheless, because of MFA implementation on the focused firm, the attackers couldn’t instantly entry the community with the stolen credentials. Utilizing Distant Desktop Protocol (RDP) from a number of firms in proximity, the attackers have been in a position to compromise and use privileged authentication credentials to hook up with the focused firm community. The assailants have been in a position to get across the meant firm MFA units by daisy-chaining collectively much less safe entry factors from close by firms and exploiting a multihomed community together with the CVE-2022-38028 vulnerability permitting Home windows Working System privilege elevation through the print spooler software program. A multihomed community is one which connects a number, machine, or laptop concurrently to a couple of community. Within the case of this multihomed community, Web connectivity was offered through a wired Ethernet connection, nonetheless, it additionally offered a Wi-Fi community adapter that could possibly be used concurrently. Whereas Web-facing sources required MFA, the Wi-Fi was not protected with MFA. In consequence, APT28 have been in a position to scan for out there networks inside vary of the Wi-Fi community adapter and connect with the goal firm enterprise Wi-Fi using the compromised credentials. As talked about beforehand, this assault didn’t require {hardware} to be positioned within the neighborhood of any one of many compromised networks or the businesses’ bodily areas. The absolutely distant assault was executed in its entirety from the opposite aspect of the globe utilizing solely software program vulnerabilities and exploitations to acquire privileged credentials and entry the focused firm community and knowledge that it contained.
Mitigations of such exploitations ought to embrace implementation of sturdy encryption and safe wi-fi channels for MFA codes and machine communications, employment of multi-device MFA methods, institution of sturdy entry controls, exercise monitoring, incident response processes for MFA units and techniques, and common updates to MFA software program and firmware to deal with identified vulnerabilities. Intensive consideration must also be given associated to potential dangers that Wi-Fi networks might current to safety.
Purposes and Concerns for Nationwide Protection
For protection purposes, the position of software program safety in wi-fi communication techniques is essential. Trendy warfare requires wi-fi communications for command and management (C2), situational consciousness, autonomy, and distributed engagement in a variety of environments. Lack of communication capabilities will virtually actually lead to mission failure. To thwart C2, adversaries will aggressively search methods to disclaim communications. With rising scope, complexity, distribution, and connectivity of wi-fi communication techniques and systems-of-systems, the potential assault floor continues to increase dramatically. An correct understanding of the software program that makes up these techniques is more and more vital, from low-level code and libraries to software-defined radios and networks, as much as and together with the appliance layer interfaces, and all components in between.
There are extra issues for protection equivalent to
- adversarial threats: Adversaries may intentionally intrude with communication techniques to disclaim, degrade, or disrupt connectivity in addition to search means to extract important info/knowledge.
- useful resource constraints: With rising quantities of knowledge required for modern-day warfare, mission ways, strategies, and procedures should be sufficiently environment friendly to execute on edge units with restricted connectivity, computing energy, and storage.
- impression: Communication system failures, both through connectivity or loss/theft of data, can have substantial impression on important operations, probably leading to lack of knowledge, sources, and lives.
Work with the SEI
Understanding the position of software program and safety in wi-fi communication techniques is step one in direction of mitigation to make sure covertness and robustness. Right here on the SEI, we’ve got experience and expertise in each software program and RF engineering, and we’re repeatedly evolving processes and instruments to establish, assess, and strengthen the safety of wi-fi communication techniques. For instance, we’re researching the appliance of machine studying and synthetic intelligence strategies throughout every layer of the OSI stack together with
- PHY layer propagation prediction and channel estimation
- slice administration of software-defined networks
- wi-fi communication system autonomy
- optimizing end-to-end communications and High quality of Service
- knowledge compression and encryption optimization for wi-fi.
As well as, SEI researchers are establishing wi-fi experimentation ranges that present processes, instruments, and knowledge pipelines to establish and examine potential safety dangers throughout all layers of the wi-fi OSI stack. This work will likely be more and more vital because the disciplines of conventional cybersecurity operations and wi-fi communications proceed to maneuver in direction of convergence. To be taught extra about our work researching, testing, and evaluating software program and safety in wi-fi communication techniques or to collaborate with us, please e mail data@sei.cmu.edu.

